Understanding the vulnerabilities in your IT infrastructure is the first step to managing them. Adversaries use system weaknesses – including unpatched software, poorly configured services, default passwords or exposed services – to compromise an IT estate, leaving your business vulnerable to attack.
Using best in class technology, CORVID's Vulnerability Scanning tool routinely scans your entire estate to identify potential vulnerabilities. This information is used by our security analysts to provide an easy to understand monthly report, offering clear, actionable intelligence and remediation advice on how to resolve any potential issues.

CORVID’s proactive attack surface management service routinely scans all network connected devices using one or several engines hosted in your own infrastructure, with secure connectivity back to CORVID. The data received is checked against our database of vulnerabilities and interpreted by our security analysts who, after taking account of current attack trends, identify the most pertinent vulnerabilities and compile a custom report detailing the results of the security scan, with actionable advice to identify and patch vulnerabilities.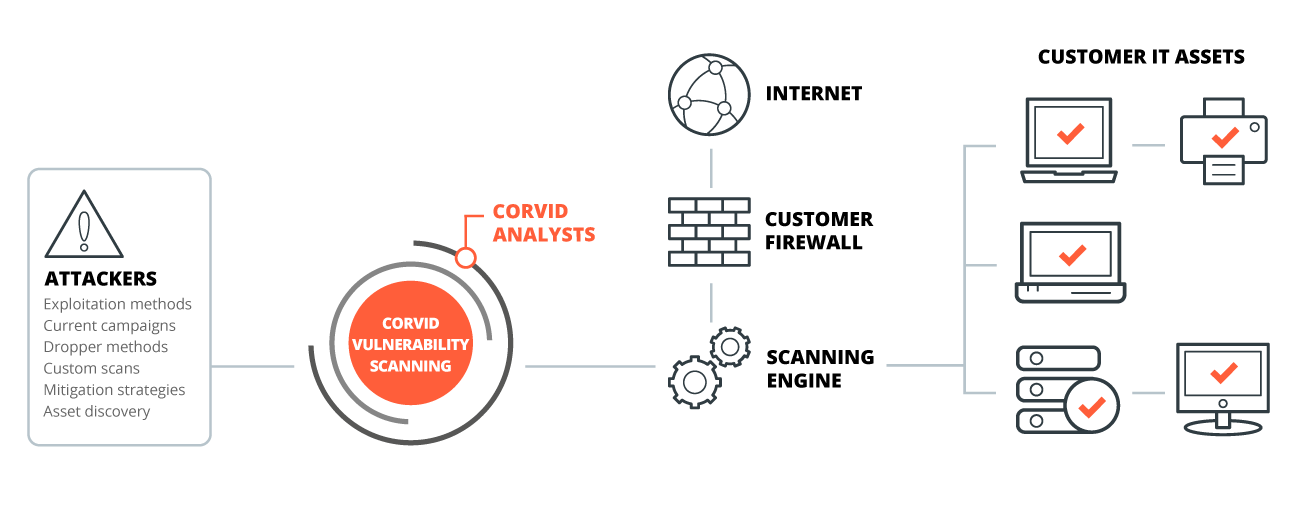
Cyber attacks are inevitable, and safeguarding your IT infrastructure takes time, effort and dedication. CORVID Vulnerability Scanning makes the daily management easier. With smart security scanning, you gain a true picture of your attack surface, to determine where resource is best placed.
CORVID Vulnerability Scanning is an essential service that can be implemented as a standalone cyber security solution, or can complement and work seamlessly alongside the full CORVID Managed Detection and Response service for complete peace of mind.